The main problem with smart cards is lack of secure display and keyboard that would allow users to verify data sent to the smart card from their computer. Malware on the computer may then alter the data and, for example, change the recipient of a bank transfer.
Continue reading Trusted Path for Smart CardsCategory Archives: passwords
Transaction Security with Slow Clock and Counter – How to Conjure Up Entropy
I love cryptography. It’s an abstract science, where I can define a problem, come up with a solution and prove it (eventually). I also like applying cryptography as it involves real world (users, limitations of computers, …), which messes everything up and turns pure mathematics into a fun game. Continue reading Transaction Security with Slow Clock and Counter – How to Conjure Up Entropy
Password Attacks – A Small Server Experiment
This short post looks at passwords attacks that were launched during 5 months’ period against a small web server of ours in 2013.
There are a lot of statistics about what is the most prolific passwords we use to login to our online accounts. What we were interested in was what passwords are being used to guess logons to online systems. We setup a WordPress website and started logging passwords tried against that website. Here are some results after about 5 months of monitoring and over 11,000 of logged attacks.
Continue reading Password Attacks – A Small Server Experiment
Why Storing Plaintext Passwords Is Bad
No matter what bad news we hear about passwords – leaks, security breaches, compromised security – passwords provide a very good protection when used properly. The real weak link here is the user. If users could remember long and random passwords, the “problem of passwords” would be much, much smaller. The hype would disappear and the real issue – how internet companies store passwords – would become much move visible.
“One time passwords” are not passwords
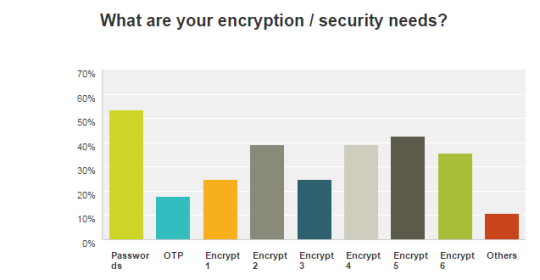
We did a bit of research into what IT start-up companies need in terms of security. I did expect that secure authentication / logons would be at the top but I was surprised that OTP (one time passwords) were at the bottom.