In fact, Office 365 is a form of a virtual network for a particular use. The question is if we can create “private spaces” different use cases: remote access to home “Wi-Fi”, anonymous access to the internet, team sharing space, …
 The initial idea came from an observation that it took us more than a day to set up a virtual private network (VPN) server from scratch. Also, if you don’t want to use yet another password, then a part of the setup is to start generating keys and issuing certificates. As we already have a key management system we just connect somehow the two things together.
The initial idea came from an observation that it took us more than a day to set up a virtual private network (VPN) server from scratch. Also, if you don’t want to use yet another password, then a part of the setup is to start generating keys and issuing certificates. As we already have a key management system we just connect somehow the two things together.
We have discussed the “connect somehow” for a while and made a list of options. We wanted something simple, just one UI for the whole thing and without much additional setup.
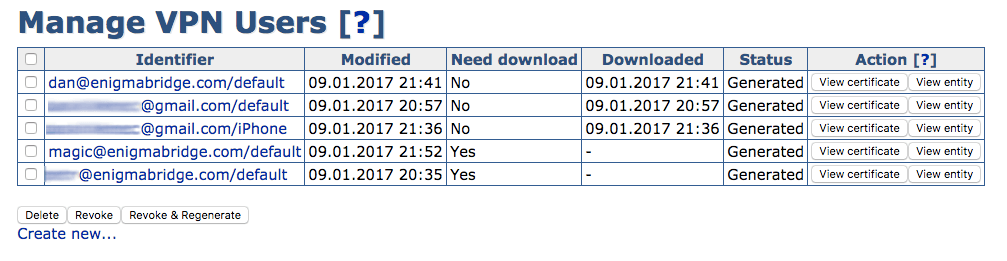
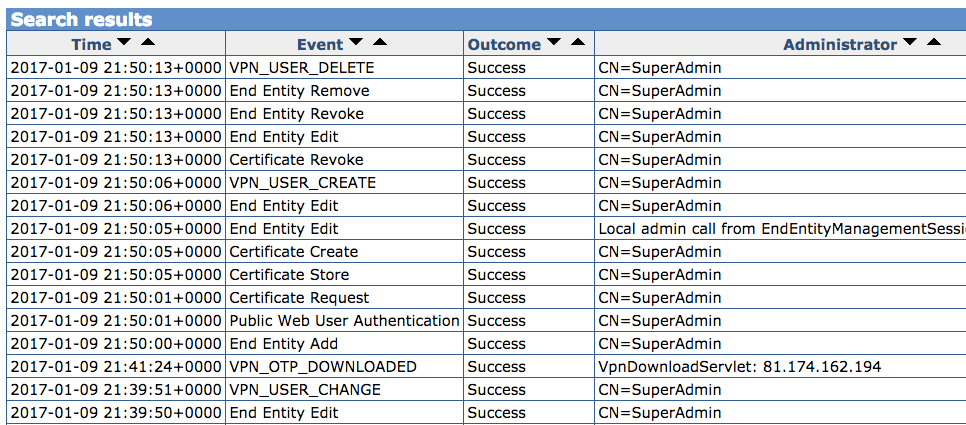
 The winner was an extension of the key management system (EJBCA) to include management of VPN users. I am very lucky to work with guys who not only can pick a winner, but then get their heads down and implement it. So here we are, a few weeks later and we have the first screenshots of how it works.
The winner was an extension of the key management system (EJBCA) to include management of VPN users. I am very lucky to work with guys who not only can pick a winner, but then get their heads down and implement it. So here we are, a few weeks later and we have the first screenshots of how it works.
How it works – the flow
You may have heard of similar projects before. Streisand has been around for 3 years now. Once installed, it offers a number of services, including a Tor bridge for anonymous web access. A recent project Popup OpenVPN builds a VPN server on DigitalOcean. Both of them start by installing a git client – not quite the easiest first step for “just a user”.
We decided to build Enigma Private Cloud Space on top of our Amazon key management system (PKI), with user registration built into the PKI web administration interface. It uses password-less VPN connections (based on certificates instead), and includes an automated configuration of its security and a professional key management system. This makes it more suitable for small businesses or professional use.
The initialization starts in the Amazon AWS control panel.
- We provide a link to launch a new virtual machine (EC2). You just select the size of it, and the authentication key to connect to the new EC2 instance with terminal.
- Once your new instance is launched, you need to connect with a terminal and stat initialization of the private space – it’s a simple “ebvpn” and “init” as its internal command.
- You will be asked for an email address so we can send to you details of your private space (and the VPN server).
- You can now nip out for lunch or a cup of coffee and in some 20 minutes, the VPN server should be ready.
- You download a file with a client, HTTPS key for login to the web user interface and you can also create a support client account.
Once you login to the EJBCA system, you can start adding new users to your Private Space. All you need to provide is an email address and a name of the device, which you want to use to connect to the Private Enigma Space.
All configuration bits and bobs (a key, certificate, and a configuration file) are completed automatically, and a download link is emailed to the user – the link can be used only once.
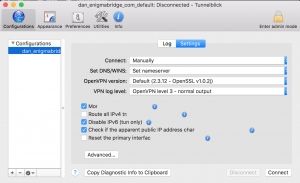
User needs to install a VPN client – there are free clients for all mobile and computer platforms – and open the configuration file. This will automatically configure the device.
Once completed, the VPN connection needs to be enabled and users can start connecting to your internal network.
The default configuration also includes a dynamic DNS so you can easily set up your intranet / home / office network to connect to the Private Space using a particular domain name you get.
Sounds interesting? Let me know! [contact-form subject=’Private Cloud Space ‘][contact-field label=’Who you are’ type=’text’ required=’1’/][contact-field label=’Message’ type=’textarea’ required=’1’/][/contact-form]